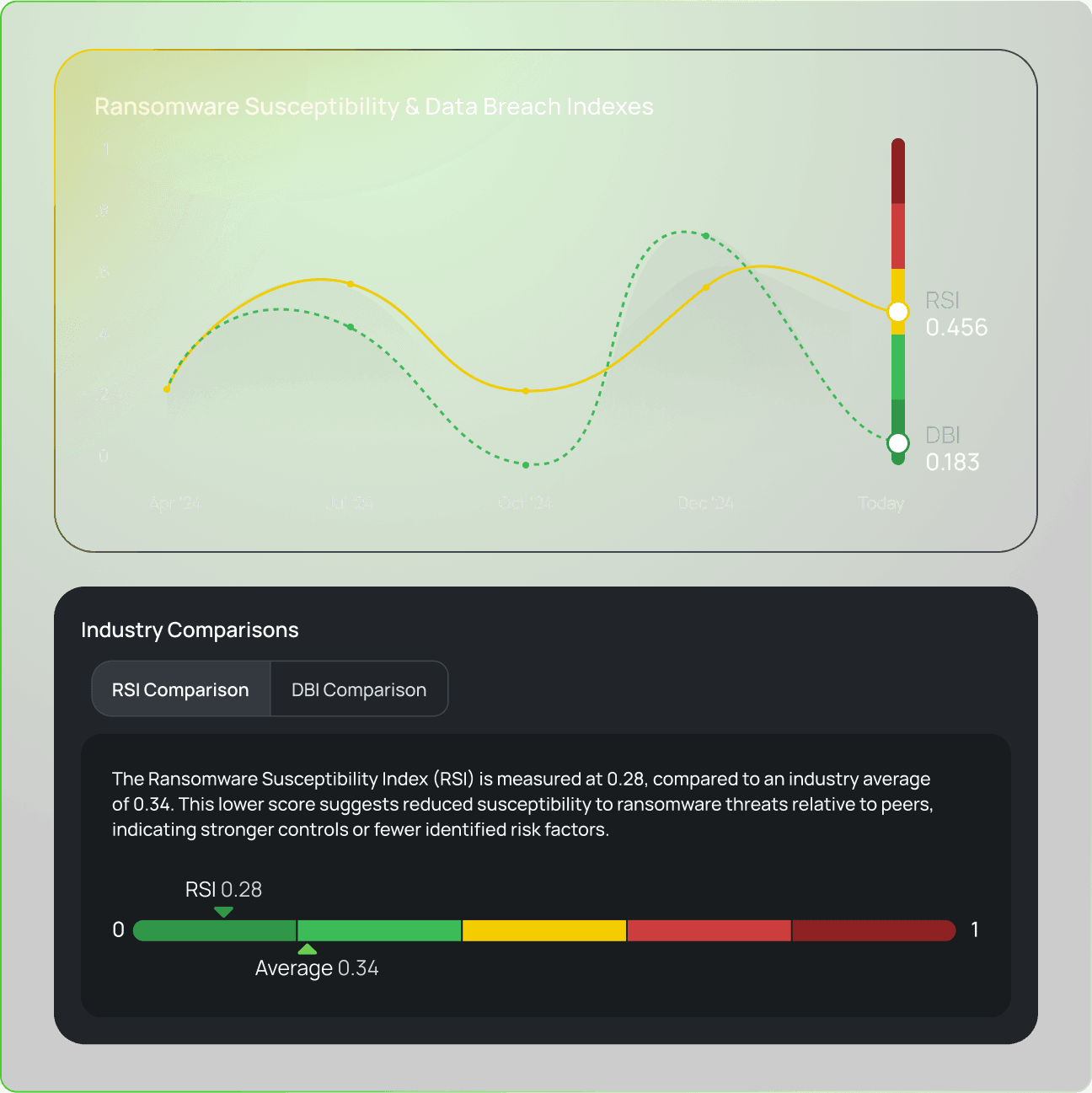
Point-in-Time Assessments Miss Emerging Threats
Cyber risk doesn’t stop after onboarding. Vendors evolve. New threats emerge. Hidden dependencies surface when you least expect them. In between scheduled assessments, critical vulnerabilities may already be exploited. While assessments remain an essential component of a TPCRM program in supporting compliance requirements, framework alignment, and deeper control validation, they don’t reflect a vendor’s real-time risk profile. Relying on point-in-time assessments alone create blind spots that delay detection and response.